Kubernetes - Create a staging site for each branch
How to create a unique staging environment for each branch by using kubernetes
Terraform - Place your EC2 instance in a private subnet
Looking at different ways we can connect Redshift and Lambdas inside of a private subnet to SecretsManager
Kubernetes CKAD Exam Tips
Top 4 tips for passing the k8s CKAD exam
How to configure Magento2 environment variables
Let’s look at the correct way to configure environment variables in magento 2
How to restrict access to a single S3 bucket
We look at how to create a policy for giving full access to a single S3 bucket in AWS
Using Postman with Magento the right way
Magento’s API uses an expiring bearer token for authorization. This means that you will need to routinely pull down a new bearer token in order to keep using the API.
Magento Tips - Pentest with sqlmap
How do I test my magento site for common sql injection vulnerabilities
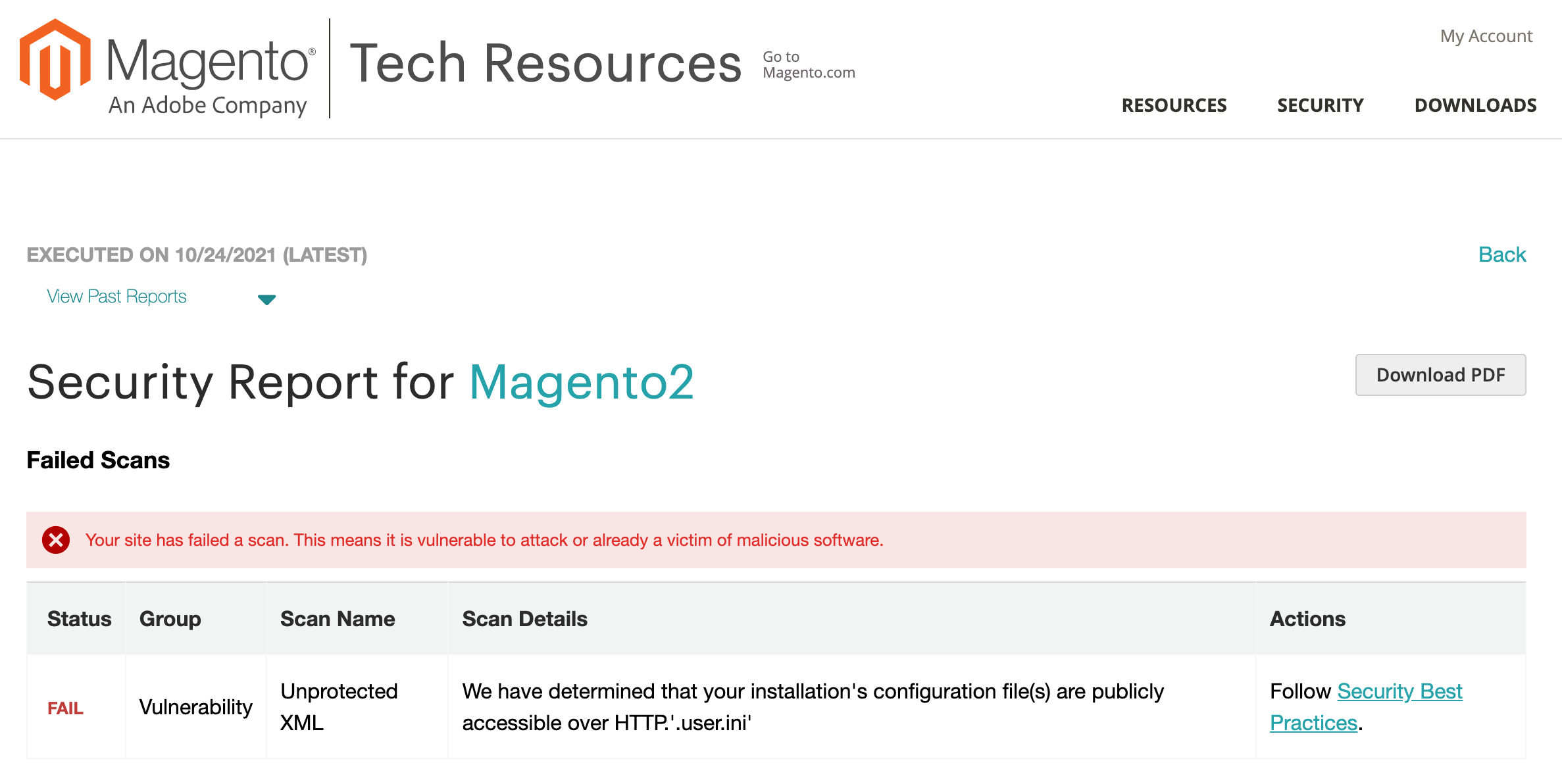
Magento Tips - Solve .user.ini issue
How to solve the .user.ini issue raised by the Magento Security Scan
Magento Tips - List All Modules
How to list all installed module versions quickly
Docker Tips - UFW
By default docker will override UFW, it is important to be aware of this so that you do not expose your docker containers to the world.
Nginx Tips - Rate Limit Url Map
Rate limit specific pages using nginx
Magento Tips - Log Rotate
Stop your magento log directory overflowing with this one simple script
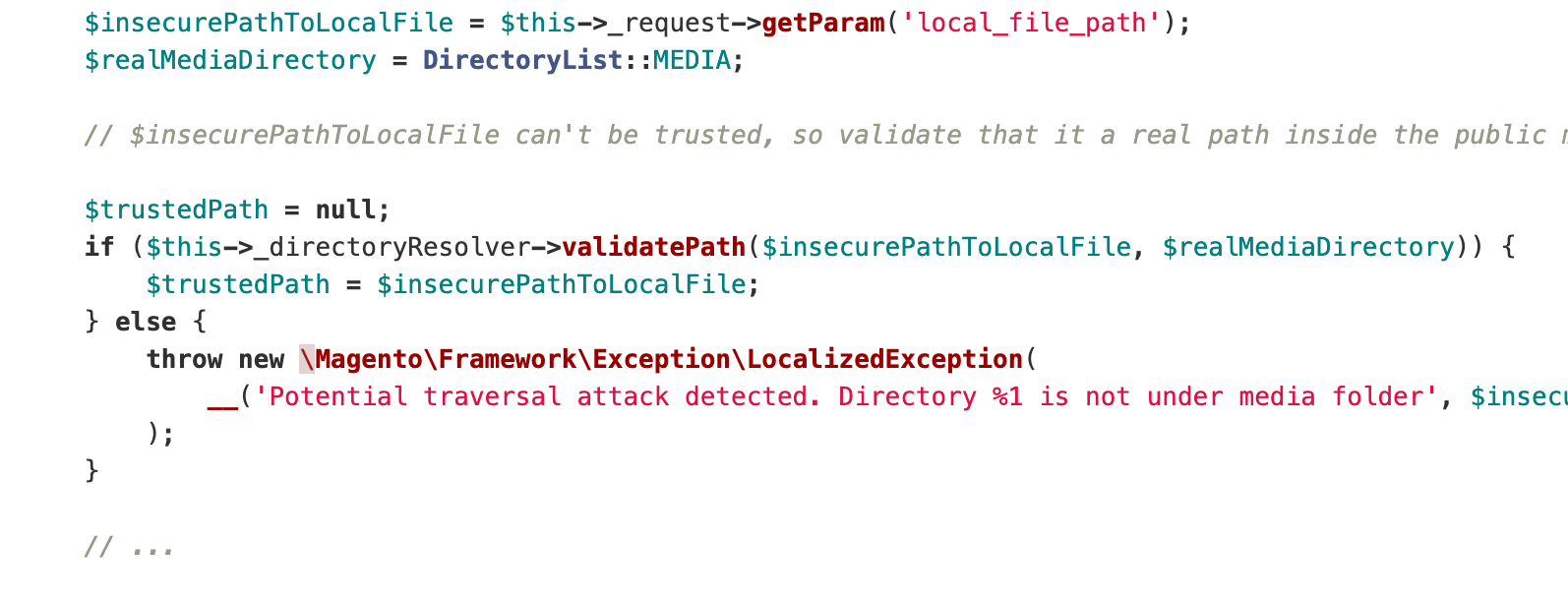
Prevent traversal attacks in Magento 2
As a rule of thumb, never roll out your own security. If you have a modern framework at your disposal then it is much easier to follow their best practice.
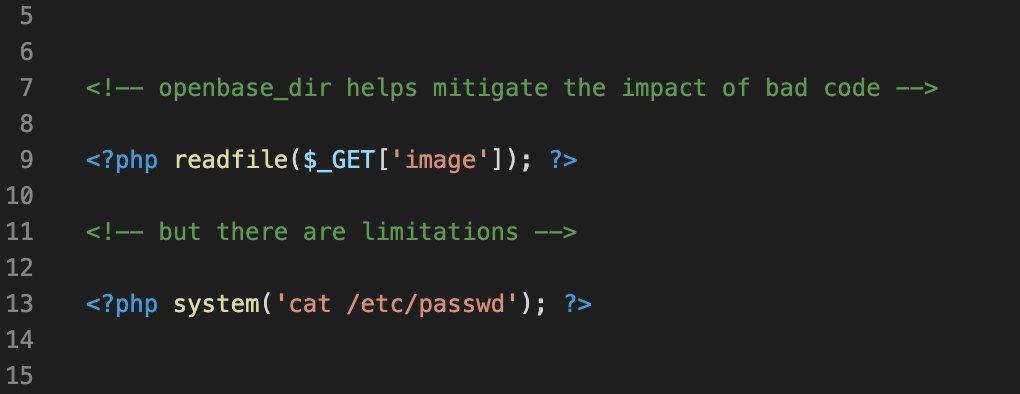
PHP Security Tips - open_basedir
This feature takes seconds to configure, and adds a layer of protection in the case of a directory traversal vulnerability.
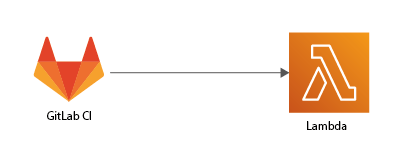
Adding Continuous Deployment to your Golang Webhook (Part 2)
So you have your infrastructure set up, the next step is to create secure automated deployments.
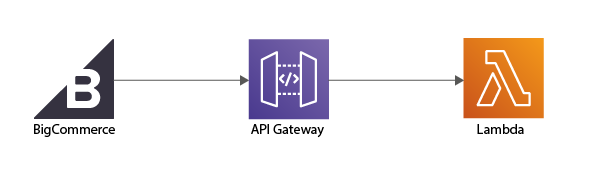
Terraforming your Golang Webhook (Part 1)
In this article we will look at how to host a serverless golang webhook by using Terraform.